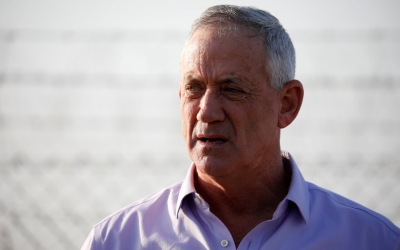
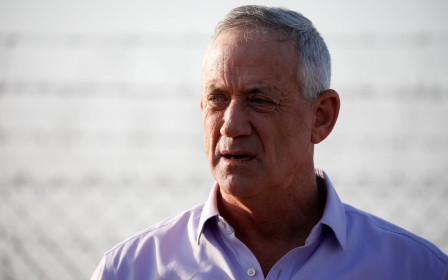
Iran denies hacking phone of Israeli election candidate Gantz

Iran has denied an Israeli media report that its intelligence service had hacked the mobile phone of Benny Gantz, the main challenger to Prime Minister Benjamin Netanyahu in next month's election.
The hack, which was first reported by an Israeli TV station on Thursday, was not confirmed or denied by the Israeli national security agency Shin Bet.
The report has been aired repeatedly by Netanyahu's Likud party in a bid to cast Gantz, former head of the Israeli armed forces, as weak on security and possibly vulnerable to blackmail.
Gantz, the leader of the Blue and White party, confirmed that his phone was hacked but said it carried no sensitive information. He has not blamed Iran.
Answering a question about the report, Iranian foreign ministry spokesman Bahram Qasemi said that "the [Israeli] regime's officials are long used to spreading lies," according to the state news agency IRNA.
Stay informed with MEE's newsletters
Sign up to get the latest alerts, insights and analysis, starting with Turkey Unpacked
"They use their propaganda tools to link any event in the world to Iran."
Qasemi said the allegations were part of an Israeli "psychological war" aimed at stoking hostility.
'Political gossip'
On Monday, Tamir Pardo, a former Mossad chief, said the leak was "a terror attack on the democratic game" and should be investigated.
"Use of classified intelligence for political purposes is a very serious matter," Pardo was quoted by Haaretz as saying to an audience at a security conference.
"Leaking an incident of this sort at the height of an election campaign breaks all the rules of the democratic game."
The journalist who first reported on the hacking has denied that the leak came from Netanyahu.
The report said that Gantz was approached six weeks ago by Shin Bet officials who told him that his phone had been hacked by Iran following his formal entry into politics in December.
They warned Gantz that if he won the election, his and Israel's security could be compromised.
At a hastily convened news conference near the Gaza border following Israeli air raids on Friday, Gantz was forced to handle awkward questions over whether he had engaged in any previous conduct that could leave him vulnerable to blackmail in the future.
Gantz dismissed the news of the hacking of his phone as "political gossip" and questioned the timing of the report, which came as his party has seen its lead over Likud slip in the polls ahead of the 9 April election.
Asked if there was anything embarrassing on his phone, Gantz said he would not dignify such "ethical nosiness" with a response.
His party had said earlier that there were "no embarrassing videos" on the phone.
Asked if the phone contained material relating to any relationship with a woman that might be used to extort him, he dismissed the idea.
"Someone is pushing this spin, and turning the real problem into one that does not exist," he said.
Gantz, 59, suggested the story had been deliberately leaked by Netanyahu.
A spokesman for Netanyahu's Likud party said they were not involved.
Shadow war
Iran and Israel have long been locked in a shadow war.
Israel and the United States are widely suspected of deploying the Stuxnet malware, uncovered in 2010, that sabotaged components of Iran's nuclear programme.
Meanwhile, Iranian hackers have been behind several cyber attacks and online disinformation campaigns in recent years as Tehran tries to strengthen its clout in the Middle East and beyond, a Reuters report published in November found.
The European Union digital security agency said in January that Iran was likely to expand its cyber espionage as its relations with Western powers worsen.
Qasemi also denied reports by Australian media in February that attempts to hack into the Australian parliament's computer network originated from Iran.
Middle East Eye delivers independent and unrivalled coverage and analysis of the Middle East, North Africa and beyond. To learn more about republishing this content and the associated fees, please fill out this form. More about MEE can be found here.